Today I'm doing an assessment on my girlfriend's Wi-Fi router (with permission of course). I'm going to be using Kali Linux and fern-wifi-cracker to capture a WPA handshake and test a wordlist against it.
Prerequisites
- Kali Linux
- fern-wifi-cracker (installed by default on Kali)
- Wireless internet adapter that supports monitor mode and packet injection
rockyou.txtor whatever wordlist- Wi-Fi router (2.4 GHz band for this test)
- At least one device set to autoconnect to the Wi-Fi
Adapter issues I hit (and the fix)
I had some issues at first with my Wi-Fi card, but ran the following commands and that fixed it.
# delete the monitor iface
sudo ip link set mon0 down
sudo iw dev mon0 del
# replace phy1 with whatever you saw in `iw dev`
sudo iw phy phy1 interface add wlan0 type managed
sudo ip link set wlan0 up
# kill existing iface
sudo airmon-ng check kill
sudo iw dev wlan0 interface add wlan0mon type monitor
sudo ip link set wlan0mon up
# sanity
iw dev
iwconfig # wlan0mon should say Mode:Monitor
sudo airodump-ng wlan0mon
# launch fern as root
sudo fern-wifi-cracker
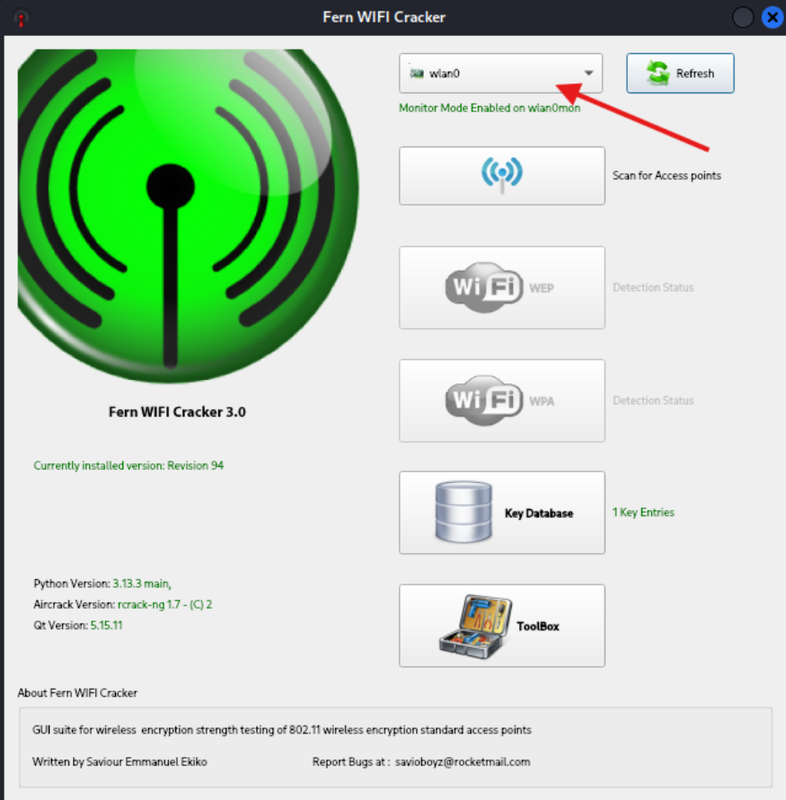
Point and click in Fern
Once the GUI appears, select your wireless card:
Then, start scanning for access points:
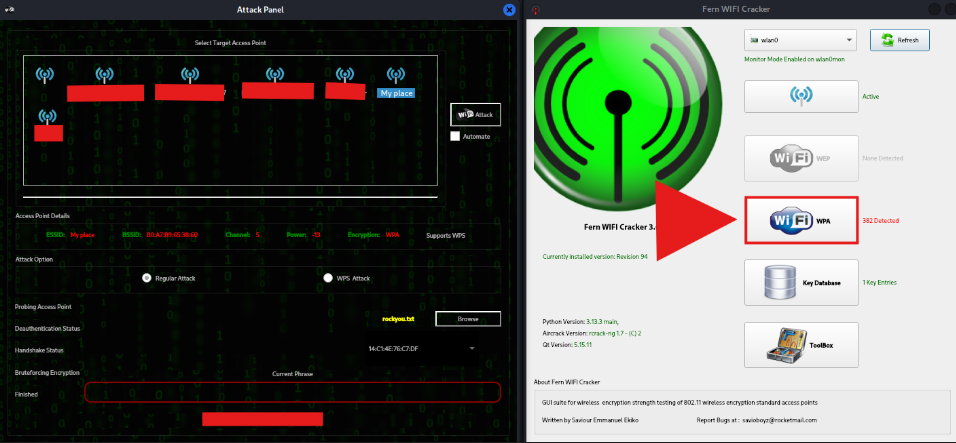
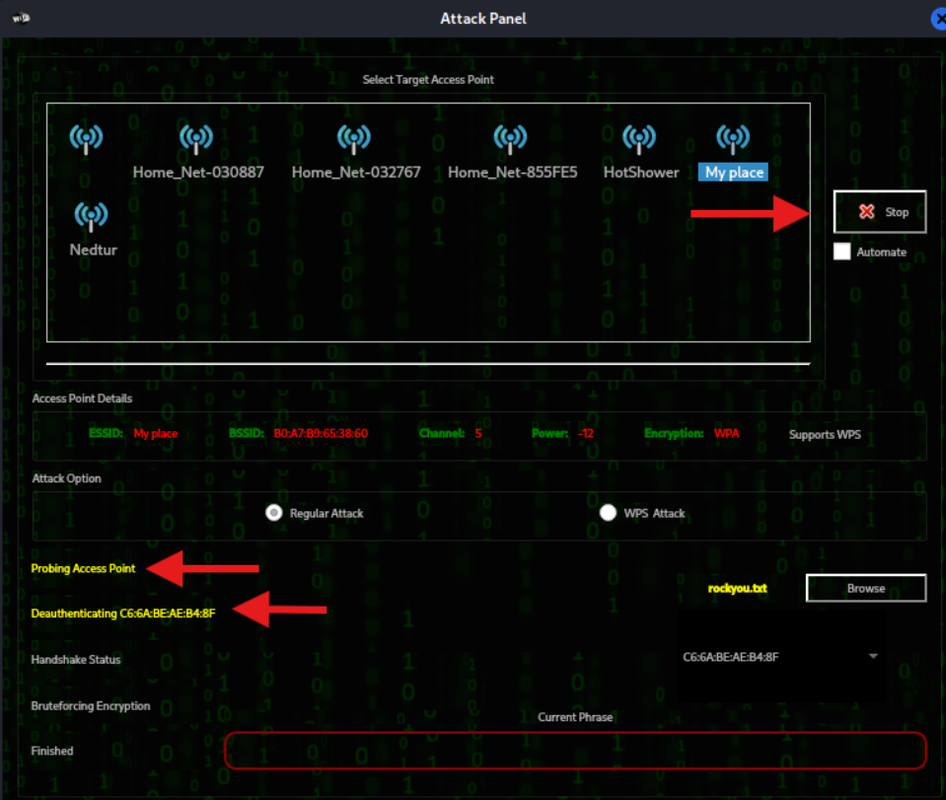
Once the access points start to load, click on Wi-Fi WPA to load the attack panel:
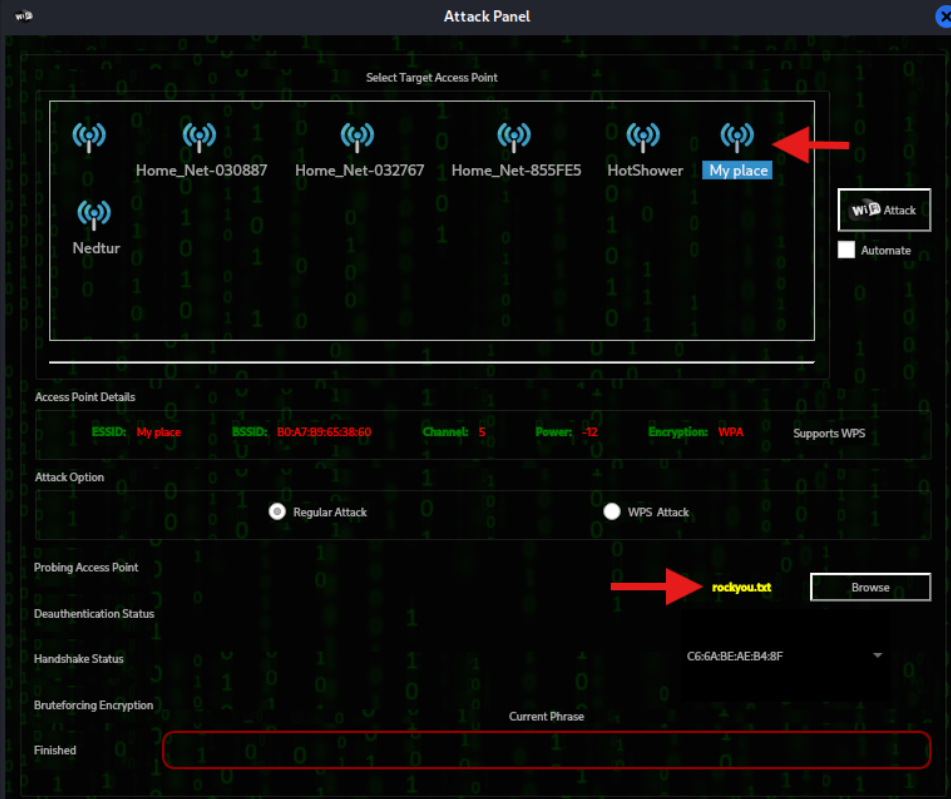
Select the target and set your wordlist for brute-forcing passwords.
Once you've set these options, click on Wi-Fi Attack:
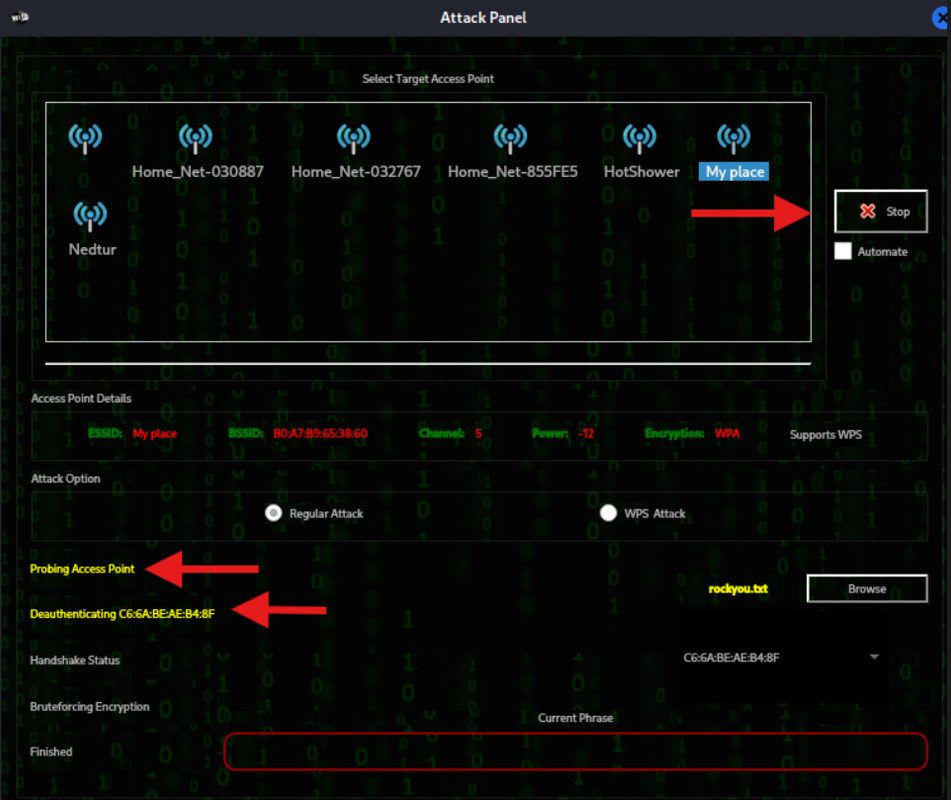
Fern will start probing the access point to find the MAC address of connected devices, then attempt to deauthenticate those devices in order to capture the handshake upon reconnecting. From the target device's perspective, it will disconnect and reconnect. That can look like normal network hiccups, but it's your deauth doing its thing, so do this only with permission.
Once it successfully captures the handshake, it will start trying passwords from the wordlist. Depending on signal strength and the list, you might need more than one try.
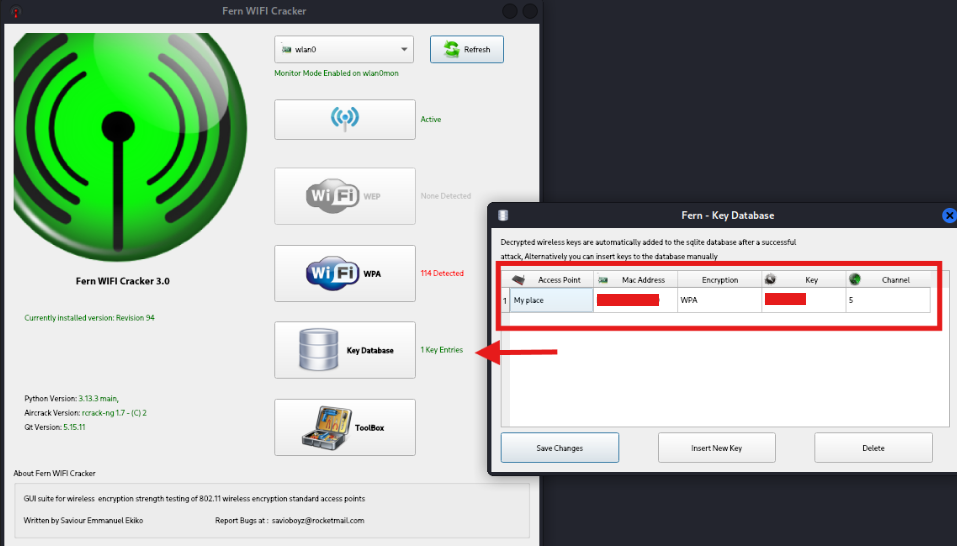
If the password is in the list, Fern will find it and store it in its database.
Notes
- 2.4 GHz was used here because many cheap adapters behave better there. Band choice isn’t security; the auth protocol and passphrase strength are.
- If you get no handshakes, check distance/interference, try a different adapter or antenna, and confirm clients are actually connected and set to autoconnect.
Lessons learned
- Use WPA2-PSK with a long random passphrase at minimum; WPA3-SAE if your gear supports it.
- Disable WPS. It’s low-hanging fruit on a lot of routers.
- Consider not enabling auto-connect on devices for networks you care about. It makes forced reconnects easier to exploit.
- 5 GHz reduces range and congestion, which helps in practice, but it doesn’t “secure” the network by itself.
- Keep firmware updated. Vendors do patch real Wi-Fi security bugs.
Only test networks you own or have explicit permission to assess. Capturing handshakes and forcing reconnects on someone else’s network is illegal. Document what you do and keep it tight.